
If you’re not a technology expert, cybersecurity can feel confusing—much like trying to understand complex topics as a kid. The good news is that it doesn’t have to be overwhelming. The National Institute of Standards and Technology’s (NIST) Cybersecurity Framework (CSF) offers a practical starting point to help you understand cybersecurity and how to protect your organization.
So, what exactly is the NIST CSF?
The NIST CSF is a set of guidelines and best practices designed to help organizations improve their cybersecurity posture. It provides a structured approach to managing and strengthening security programs. While it is not a one-size-fits-all solution, it is flexible and can be adapted to meet the needs of organizations of any size or industry.
The 5 Elements of NIST CSF
To get started, it’s important to understand the five core functions of the framework:
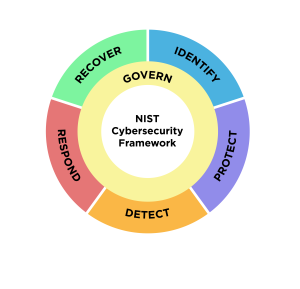
1. Identify
This function emphasizes the importance of understanding your cybersecurity risks before you can address them. Organizations need clear visibility into their assets, systems, and data. It also involves identifying users and their roles, as well as understanding the business processes that support critical operations.
2. Protect
Protecting your organization requires implementing strong security controls. These controls are designed to prevent, detect, and reduce the impact of cyber threats. Depending on your needs, this may include tools such as firewalls, intrusion detection or prevention systems, and encryption. The goal is to safeguard your systems and data from potential attacks.
3. Detect
Timely detection is essential in minimizing the impact of cybersecurity incidents. Organizations need visibility across their networks and systems, along with monitoring capabilities to identify unusual activity. Having the right tools and processes in place ensures that threats can be identified quickly.
4. Respond
How your organization responds to a cybersecurity incident can significantly affect the outcome. A well-defined response plan helps contain the issue, reduce damage, and restore normal operations as efficiently as possible.
5. Recover
Recovery focuses on restoring systems and data after an incident. This includes having a plan to recover lost information and resume operations quickly. It also involves clear communication procedures so employees understand their roles during and after an incident. Recovery planning is a critical part of any cybersecurity strategy.
How we help
While the NIST CSF is a comprehensive framework, not every organization needs to implement the entire framework. An IT service provider can help you determine which elements are most relevant to your business and apply them effectively.
With the right guidance and expertise, you can strengthen your defenses against evolving cyber threats. Contact us today to schedule a no-obligation consultation.
If you’re ready to take control of your IT strategy, schedule a 30-minute call to see how we can help.
Every day without a clear IT plan can lead to missed opportunities and increased risk. Now is the time to put the right strategy in place and ensure your technology is working for you, not against you. If you would like to learn how the IT professionals at SinghIT can support your business and help your business grow with confidence, contact us today at (437) 880-2051.

